Imagine arriving at your job site on a Tuesday morning to find that a $20 million development project has ground to a complete halt because a single ransomware attack locked every blueprint and bid document on your server. In 2024, data from the Cybersecurity and Infrastructure Security Agency (CISA) indicated that construction firms are increasingly frequent targets for digital extortion, with recovery costs for some mid-sized firms exceeding $450,000. Protecting your firm requires specialized construction cybersecurity solutions that understand the unique pressure of tight deadlines and the inherent risks of field workers using personal devices on remote sites.
You already know that managing a complex build is a logistical marathon, and the last thing you need is a security breach causing expensive downtime. We believe your technology should act as a silent, efficient partner that eliminates worry rather than creating it. You’ll discover how to secure your digital perimeter, maintain strict compliance with US data protection standards, and provide your team with seamless access to critical files from any location. This guide outlines the proactive steps needed to ensure zero downtime and total infrastructure stability for your business.
Key Takeaways
- Understand why Canadian construction firms are primary targets for ransomware in 2026 and how to safeguard your critical CAD files and bid data.
- Learn how to implement a multi-layered defense using proactive construction cybersecurity solutions that protect your firm’s identity, network, and endpoints simultaneously.
- Discover how Managed Detection and Response (MDR) provides 24/7/365 vigilance that far exceeds the capabilities and coverage of a traditional in-house IT model.
- Get a practical checklist for securing digital job sites, including effective BYOD policies and secure connectivity for field operations across Ontario and beyond.
- Explore how a “Security First” onboarding process with a local partner like Reis Informática ensures your infrastructure remains resilient while you focus on your core business.
The Rising Stakes of Construction Cybersecurity in Kitchener, Waterloo, and Calgary
In 2026, building a legacy in the Canadian construction sector requires more than master craftsmanship; it requires a “Digital Foundation” that is as stable as the concrete you pour. Construction cybersecurity is the specialized practice of protecting your firm’s digital assets from unauthorized access. These assets include your proprietary CAD files, sensitive bid data, and the payroll details of your entire workforce. Just as you wouldn’t leave a multi-million dollar job site unlocked overnight, you can’t afford to leave your network exposed to external threats. If your digital files are compromised, the physical project often grinds to a halt.
Canadian firms have become prime targets for ransomware as we move through 2026. Hackers recognize that your industry operates on tight margins and even stricter timelines. A security breach at a contractor’s office in Mississauga or London doesn’t just stay in the office. It can halt physical site operations, lock specialized machinery, and prevent teams from accessing essential blueprints. Integrating foundational cybersecurity principles into your daily operations is the only way to ensure your project stays on track. By investing in robust construction cybersecurity solutions, you protect your reputation and your bottom line from invisible threats.
Why the Construction Industry is a Top Target
High-value transactions and time-sensitive deadlines provide immense leverage for cybercriminals. If a project is worth C$50 million and is days away from a critical milestone, an attacker knows you’re more likely to pay a ransom to avoid catastrophic delays. This creates a “Supply Chain Ripple Effect” where a single compromised subcontractor can jeopardize the data and safety of the general contractor and the end client. For a mid-sized Canadian construction firm in 2026, the cost of downtime following a cyber incident typically averages C$18,500 per day when accounting for idle labor, equipment rentals, and contractual delay penalties.
Regional Risks: From the Waterloo Tech Corridor to Calgary’s Energy Projects
The Kitchener-Waterloo region is experiencing a surge in smart-building projects, which significantly increases the attack surface for local firms. As you adopt more IoT devices and cloud-based project management tools, your vulnerability grows. In Calgary, the focus is often on protecting proprietary engineering data for massive energy and infrastructure projects. Meanwhile, firms in Halifax are dealing with increased risks related to maritime construction data. You must also navigate local compliance standards, such as Ontario’s privacy regulations and Alberta’s PIPA. Our construction cybersecurity solutions are designed to meet these specific regional demands while keeping your daily operations seamless and secure.
Essential Components of Modern Construction Cybersecurity Solutions
Effective construction cybersecurity solutions don’t rely on a single lock. They use a multi-layered approach to protect your identity, your devices, and your network simultaneously. Think of it like a job site with perimeter fencing, security cameras, and locked toolboxes. If one layer fails, others stand ready to stop the intruder. This strategy ensures that a single compromised password doesn’t lead to a total business shutdown.
Managed Detection and Response (MDR) is a vital part of this defense for Kitchener and Waterloo firms. In plain English, MDR means you have a team of experts watching your systems 24/7. They don’t just wait for an alarm to go off; they actively hunt for threats. If a hacker tries to sneak into your server at 3:00 AM on a holiday Monday, MDR identifies and stops them before you even wake up. This proactive stance aligns with the NIST Cybersecurity Framework, which helps Canadian companies identify, protect, and respond to digital risks. You can explore our cybersecurity services to see how these layers fit your specific project needs.
AI now plays a massive role in spotting trouble before humans can. It monitors financial patterns and bid submissions for anomalies. For example, if a wire transfer request for C$75,000 deviates from your usual vendor payment history, the system flags it as a potential fraud attempt. This level of oversight is essential for maintaining the integrity of your supply chain and payroll.
Identity and Access Management (IAM)
Multi-Factor Authentication (MFA) is your first line of defense and it’s non-negotiable. Even if a cybercriminal steals a site supervisor’s password through “credential stuffing,” where they try leaked passwords from other sites, they can’t get in without that second code. Managing access for seasonal field workers or sub-contractors is equally vital. You must revoke access the moment a contract ends to prevent “ghost” users from leaving a back door open to your sensitive data.
Endpoint Protection for the Field and Office
Your office laptops and the tablets used on-site are all “endpoints.” Each one is a potential entry point for ransomware. Endpoint Detection and Response (EDR) goes beyond basic antivirus by monitoring device behavior. If it sees a file trying to encrypt itself, EDR kills the process instantly. Proactive server maintenance is also a must for firms hosting their own data, ensuring patches are applied before vulnerabilities are exploited by attackers.
Secure Cloud Collaboration
Architects, engineers, and contractors constantly share massive files and blueprints. Using consumer-grade file sharing is a significant risk because it lacks the encryption and audit trails required for professional projects. Our cloud services provide a secure environment where collaboration doesn’t compromise safety. Keeping your data in a controlled cloud space ensures that only authorized partners see your intellectual property. If you’re concerned about your current setup, a quick security consultation can help identify gaps in your field-to-office communication.
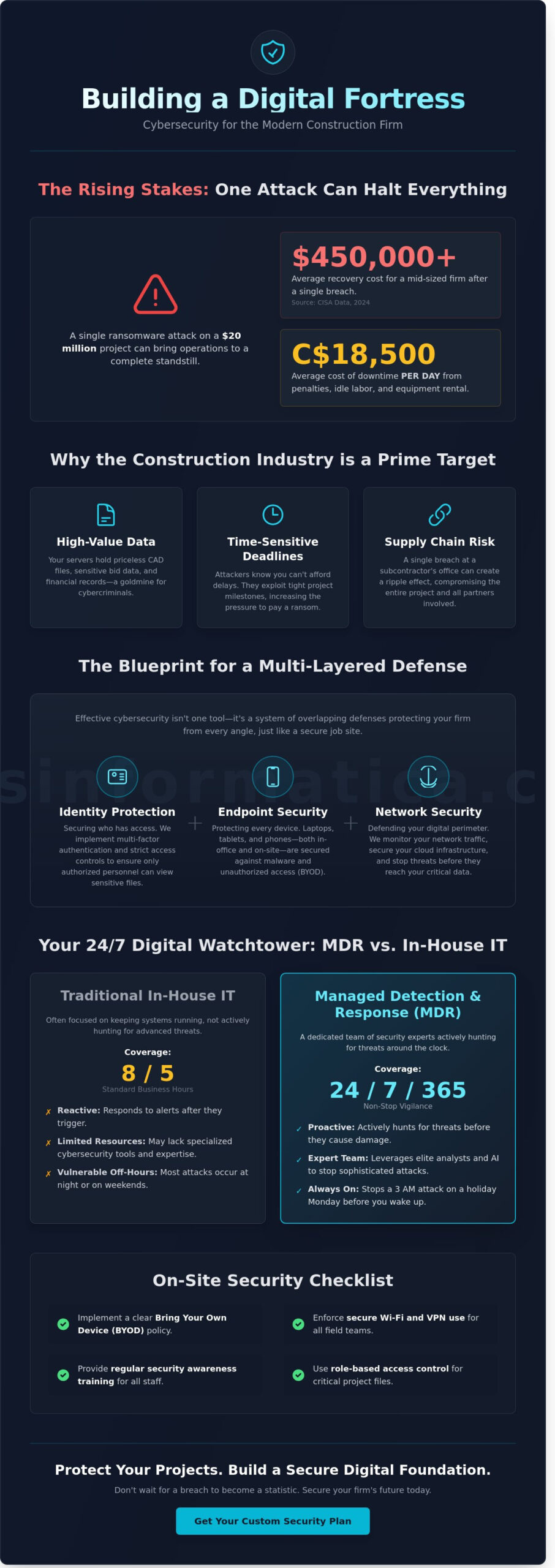
Managed Security vs. In-House IT: Choosing the Right Model
Deciding between a solo IT hire and a dedicated partner for construction cybersecurity solutions is a pivotal financial choice. A single IT manager in Ontario often commands a salary between C$85,000 and C$115,000, which doesn’t include benefits, office space, or ongoing certification costs. This individual usually works a standard 40-hour week. However, data from 2023 indicates that 71% of cyberattacks occur outside of standard business hours. Relying on one person to defend your site data at 3:00 AM on a holiday is a significant risk.
The math is simple. A Managed Service Provider (MSP) gives you access to a full team of security analysts and engineers for a fraction of a single executive’s salary. Beyond basic support, an MSP provides a Virtual CIO (vCIO). This strategic partner builds a multi-year technology roadmap, ensuring your hardware doesn’t become obsolete and your software stays compliant with Canadian privacy laws. Transitioning to managed IT services replaces the uncertainty of hiring with a scalable, professional team that never takes a sick day.
The Expertise Gap in Construction
Small and medium-sized builders in Cambridge or Milton frequently struggle to recruit specialized security talent. Most qualified experts gravitate toward large tech hubs, leaving local construction firms vulnerable. An MSP solves this through “Shared Intelligence.” When a threat is detected at one firm, the solution is immediately deployed across our entire network. This collective defense protects you from emerging threats before they even reach your inbox. A proactive IT model focuses on preventing fires rather than just being the department that shows up with a hose after the building is already burning.
Predictable Budgeting for 2026
Financial stability is the backbone of any successful project. Managed services turn volatile “emergency repair costs” into a fixed, monthly operational expense. This predictability is vital for long-term planning through 2026. Consider the ROI: the 2023 Sophos State of Ransomware report found that the average recovery cost for a Canadian organization was C$1.13 million. Preventing just one incident pays for years of professional oversight. This model aligns your IT spend with project-based revenue cycles, ensuring you aren’t hit with a massive, unbudgeted bill in the middle of a critical build phase.
- 24/7/365 Monitoring: Constant vigilance that a solo hire cannot provide.
- Scalability: Easily add seats or security layers as you win larger contracts in the Waterloo region.
- Compliance: Automated auditing to meet the strict requirements of modern construction cybersecurity solutions.
By choosing a managed model, you shift the burden of technical vigilance to a partner who lives and breathes security. This allows your leadership team to stop worrying about server uptime and start focusing on meeting your 2026 growth targets.
Securing the Digital Job Site: A Checklist for Field Operations
Construction sites in Kitchener and Waterloo are no longer just about concrete and steel. They are data hubs where tablets display blueprints and sensors track heavy machinery. This digital shift means your field operations are now the front line of your defense. Implementing specific construction cybersecurity solutions ensures that a lost device or a weak Wi-Fi signal doesn’t lead to a total project shutdown. Use this checklist to harden your job site security.
- Implement a functional BYOD policy: Most workers use their personal phones for quick site updates. You need a “Bring Your Own Device” policy that sets clear boundaries. It should define which apps are allowed for work and how company data is stored on personal hardware.
- Secure job site connectivity: Temporary Wi-Fi and satellite internet connections are common on remote sites. These networks are often vulnerable. Always change default router passwords and ensure WPA3 encryption is active to prevent unauthorized access.
- Build a Human Firewall: Technology alone isn’t enough. Field staff must understand physical device security and how to spot phishing attempts. Treat digital security with the same rigour as physical safety protocols.
- Encrypt site-to-office updates: Standard text messages are easily intercepted. Use encrypted communication platforms for all project updates, ensuring that sensitive timelines and budget data remain private.
Mobile Device Management (MDM)
If a project manager loses a tablet at a job site in Mississauga, the risk of data theft is immediate. Mobile Device Management allows your IT team to remotely wipe that device in seconds, protecting your intellectual property. MDM also allows for “sandboxing,” which separates personal photos and apps from business data on employee phones. By forcing the use of VPNs for all field connections, MDM creates a secure tunnel for data to travel between the site and your main office, regardless of the network quality.
Cybersecurity Awareness Training
Investing in training is the most cost-effective move a construction firm can make. While hardware can be expensive, teaching your team to be vigilant costs much less and yields high returns. You can find practical tips in this guide on cybersecurity awareness to help build your team’s skills. Frame this training as “digital PPE.” Just as a worker wears a harness to prevent a fall, they use strong passwords and multi-factor authentication to prevent a breach. Statistics from 2023 show that firms with regular training programs reduce their risk of a successful attack by up to 70 percent.
Protect your project data from the trailer to the boardroom. Learn more about our specialized cybersecurity services for the construction industry.
Implementing Proactive Solutions with Reis Informática
Reis Informática serves as the dedicated local partner for firms seeking robust construction cybersecurity solutions in Kitchener, Waterloo, and across the country. We believe that protecting your job site data is as critical as the structural integrity of your buildings. Our “Security First” onboarding process ensures that every new client starts on a foundation of resilience. Instead of patching holes as they appear, we build a perimeter that prevents intrusions from the start. This process involves a deep dive into your current hardware, software, and employee workflows to eliminate weak points before they are exploited.
Our team integrates advanced AI business solutions to provide constant vigilance over your network. These systems monitor traffic patterns to identify threats before they can encrypt your files or steal sensitive project bids. If a suspicious login occurs at 3:00 AM, our AI tools flag and isolate the risk instantly. We want your technology to be invisible and efficient. It should act as a silent guardian that allows your project managers and site supervisors to focus on building without worrying about digital downtime.
Our Local Commitment
While we are deeply rooted in the Kitchener-Waterloo tech corridor, our reach extends to London, Mississauga, Calgary, and Halifax. This national presence gives us a unique perspective on the Canadian business landscape and the specific regulatory requirements firms face here. A local partner understands that a delay on a Waterloo job site has ripple effects across your entire supply chain. You can begin securing your operations by scheduling a comprehensive cybersecurity audit with our specialists. This audit provides a clear roadmap of your current risks and the exact steps needed to mitigate them.
Next Steps for Your Firm
Waiting for a breach to happen before acting is a gamble that costs Canadian businesses millions. According to IBM’s 2023 Cost of a Data Breach Report, the average cost of a data breach in Canada reached C$6.94 million per incident. Proactive planning is the only way to safeguard your reputation and your bottom line. We invite you to move beyond reactive fixes and embrace a consultative partnership that prioritizes your firm’s longevity.
Don’t let your firm become another statistic in an industry report. Explore our full menu of IT services to see how we can streamline your entire infrastructure while keeping it secure. Let’s start a conversation today to ensure your construction cybersecurity solutions are as solid as the foundations you pour. Our experts are ready to help you transition to a more secure, efficient, and worry-free technological environment.
Securing Your Firm’s Future in a Digital-First Industry
The construction landscape in 2026 demands a shift from reactive fixes to proactive defense. Protecting your intellectual property and project timelines requires robust construction cybersecurity solutions that integrate directly with your field operations. By choosing a managed model over traditional in-house IT, firms in Kitchener, Waterloo, Calgary, and Halifax gain access to specialized vCIO leadership and 24/7 monitoring. This approach eliminates the risk of costly project delays and ensures your digital job site remains as secure as your physical one.
Reis Informática understands that technology should serve your business goals, not create new hurdles. Our team focuses on maintaining zero project downtime through constant vigilance and local expertise tailored to the Canadian market. We’re here to act as your strategic partner, handling the technical complexity so you can concentrate on your next major build. It’s time to replace uncertainty with a foundation of stability and professional support. You don’t have to navigate these digital risks alone when expert help is a click away.
Secure Your Construction Business with a Custom Cybersecurity Audit from Reis Informática Today
Taking this step today ensures your business stays resilient against tomorrow’s challenges.
Frequently Asked Questions
What are the most common cyber threats facing Canadian construction firms in 2026?
In 2026, Canadian construction firms face a 35 percent increase in AI-driven phishing and sophisticated ransomware attacks targeting sensitive project blueprints. Statistics from the 2024 Canadian Centre for Cyber Security report indicate that 1 in 5 small to medium enterprises experienced a cyber incident. These threats often target the supply chain, where hackers exploit vulnerabilities in vendor software to gain access to your primary network and financial data.
How much should a mid-sized construction company spend on cybersecurity solutions?
Mid-sized construction companies typically allocate 10 percent to 15 percent of their total IT budget toward robust construction cybersecurity solutions. According to Deloitte’s 2023 global survey, this often equates to roughly 0.2 percent to 0.5 percent of total annual revenue. Investing this amount ensures you have the necessary monitoring, incident response plans, and employee training to protect your firm from a breach that could cost an average of C$6.94 million per incident in Canada.
Do we really need specialized security if we use Microsoft 365?
Microsoft 365 provides a strong foundation, but it isn’t a complete security strategy on its own. While it secures the underlying infrastructure, you’re responsible for the data, identities, and device management within that environment. Specialized security layers, like advanced endpoint protection and 24/7 monitoring, fill the gaps that standard office suites leave open. This proactive approach ensures your sensitive project bids and employee records remain protected against targeted attacks.
How can I secure a job site that has limited internet connectivity?
You can secure remote job sites by implementing hardware-based VPNs and encrypted mobile hotspots that create a private tunnel for data transmission. Even with intermittent connectivity, local data encryption on ruggedized tablets ensures information stays safe if a device is lost or stolen. Establishing a zero trust policy for all site devices prevents unauthorized access to the main office network, regardless of the signal strength at the construction site.
What is the “Human Firewall” and why does it matter for construction workers?
The Human Firewall refers to employees who are trained to recognize and report cyber threats before they can cause damage. Since 82 percent of data breaches involve a human element, your workers are your first line of defense. Regular security awareness training transforms your site supervisors and office staff into a vigilant barrier against social engineering. This culture of security is just as vital as any software you install.
Can cybersecurity solutions help with our insurance premiums?
Implementing professional construction cybersecurity solutions can lead to a 10 percent to 25 percent reduction in cyber insurance premiums. Carriers now require proof of Multi-Factor Authentication and regular backups before they’ll even issue a policy. By demonstrating a proactive security posture, you prove to insurers that your firm is a lower risk. This not only lowers your costs but also ensures you have adequate coverage in place.
What happens if a subcontractor is breached-are we liable?
You may be held legally and financially liable if a subcontractor’s breach exposes shared project data or client information. Data from the 2023 IBM Cost of a Data Breach Report shows that third-party vulnerabilities are a top cause of expensive security incidents. It’s essential to include strict cybersecurity requirements in your contracts. We help you verify that your partners meet the same security standards you do to protect your reputation.
How long does it take to implement a managed cybersecurity solution?
A comprehensive managed cybersecurity solution typically takes 30 to 90 days to fully implement across your organization. The process begins with a 14-day discovery phase to identify vulnerabilities in your current systems and job site setups. Following this, we deploy security tools and conduct staff training in phases. This structured timeline ensures your operations continue smoothly while we build a shield around your digital assets.

