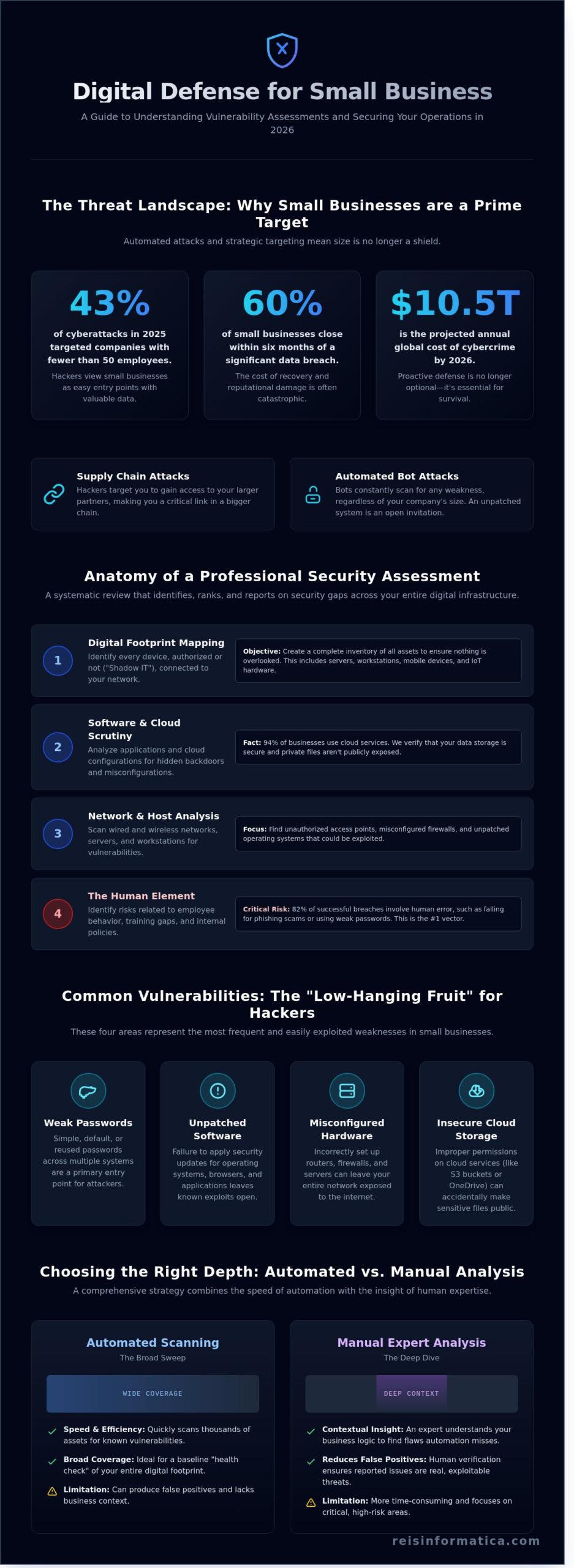
In 2025, 43% of cyberattacks across Canada specifically targeted companies with fewer than 50 employees. For a business owner in Kitchener or Toronto, that isn’t just a statistic; it’s a clear signal that the “it won’t happen to me” mindset is now a dangerous liability. You likely understand that protecting your digital assets is vital, yet the constant stream of technical jargon often makes cybersecurity feel like an expensive, confusing hurdle rather than a helpful business tool. It’s frustrating when you can’t tell the difference between a simple automated scan and a deep professional audit.
This guide will show you exactly how to perform a vulnerability assessment for small business that balances your budget with high security needs. We’ll help you secure your operations in Ontario, Alberta, and Nova Scotia while ensuring you meet strict Canadian privacy standards without the typical IT headaches. We’re going to explore the clear roadmap to choosing a security partner who acts as your vigilant guardian, letting you focus on growth while your digital defense stays rock solid.
Key Takeaways
- Learn why a regular digital “health checkup” is the foundation for keeping your business infrastructure stable and resilient against modern threats.
- Understand the critical balance between automated scanning and manual expert analysis to ensure your security depth matches your specific business needs.
- Discover how a comprehensive vulnerability assessment for small business identifies hidden backdoors in your network and software before they can be exploited.
- Identify what to look for in a security provider to ensure they understand the Canadian tech landscape and communicate in a way that makes sense for your business goals.
- See how professional security diagnostics can be transformed into a strategic technology roadmap that protects your operations and fuels future growth.
What is a Vulnerability Assessment for Small Business?
A Vulnerability assessment (computing) is a systematic review of security weaknesses within your business’s digital infrastructure. It identifies, ranks, and reports on the security gaps that could allow a hacker to access your sensitive data. Think of it as a comprehensive health checkup for your company’s technology. Just as business owners in Mississauga and Milton rely on regular diagnostics to keep their physical health in peak condition, your IT environment requires routine scans to ensure small glitches don’t turn into catastrophic failures. We prioritize this proactive approach so you can focus on your core operations without worrying about hidden digital threats.
Many people confuse this process with penetration testing, but there’s a clear distinction. A vulnerability assessment for small business is a broad scan that finds the “open doors” in your system. Penetration testing is the next step, where a specialist actually tries to walk through those doors to see how much damage they can do. For most SMBs, the assessment is the most critical first step because it provides a prioritized roadmap for fixing issues before they’re exploited. By 2026, the global cost of cybercrime is expected to reach $10.5 trillion annually; staying ahead of these threats is no longer optional for Ontario firms.
Why Your Small Business is a Target in 2026
Hackers increasingly use small firms as a “Supply Chain” trap. They target a smaller business in Kitchener to gain a foothold in the network of a much larger Canadian enterprise. You’re the bridge to a bigger prize. Additionally, automated bot attacks have become the norm in Toronto. These bots don’t care about your company name or size; they simply scan thousands of IP addresses every minute looking for a single unpatched server. If you lack a robust cybersecurity strategy, you’re just a number on a list. Beyond the immediate financial loss, 60% of small businesses close within six months of a data breach due to the massive reputation damage within their local communities.
The Core Components of an IT Security Audit
A professional audit looks at your entire digital footprint, not just the computers in your office. We examine internal and external vulnerabilities to ensure your remote workers are just as safe as your team in the Kitchener headquarters. Our process focuses on identifying “low-hanging fruit” that hackers love, such as:
- Weak or reused passwords across different departments.
- Unpatched software that hasn’t been updated since 2024 or 2025.
- Misconfigured hardware like routers or firewalls that leave your network exposed.
- Cloud storage settings that accidentally make private files public.
A vulnerability assessment for small business serves as a proactive business insurance policy that secures your digital assets before a crisis occurs.
The Anatomy of a Professional Security Assessment in 2026
A comprehensive vulnerability assessment for small business isn’t a simple one-time scan; it’s a strategic deep dive into your digital foundation. Recent 2025 data shows that 43% of all cyberattacks target small organizations, primarily because their defenses are often less sophisticated than enterprise rivals. We begin by mapping every device connected to your Cambridge or Waterloo office. This process uncovers “shadow IT” devices that employees might’ve added without authorization, which frequently lack the latest security updates.
Our team scrutinizes your business software to ensure no hidden backdoors exist for hackers to exploit. Since 94% of modern businesses now rely on some form of cloud infrastructure, we evaluate the safety of your data in both public and private clouds. A professional vulnerability assessment for small business also focuses on the human element. Because 82% of successful breaches involve social engineering or human error, we identify exactly where your team needs better training. Referencing the Cybersecurity for Small Business guidelines helps us ensure your internal protocols meet federal standards for protection.
Network and Host-Based Assessments
We perform rigorous scans of wired and wireless networks to find unauthorized access points that could lead to data theft. Our specialists analyze server configurations and workstation vulnerabilities to eliminate weak spots before they’re targeted. This proactive approach ensures your hardware isn’t the reason for a costly operational outage. You can explore our cybersecurity services to see how we build these layers of protection for local firms.
Wireless and Mobile Security Gaps
Modern offices in Calgary and Halifax face unique risks from “Bring Your Own Device” (BYOD) policies. When employees use personal phones for work, they create unmanaged entry points for potential threats. We focus on securing remote access for your Canadian work-from-home staff to keep your data encrypted and private. Outdated Wi-Fi protocols remain a liability for 70% of retail and service businesses, so we verify that your wireless setup uses the most current security standards available in 2026.
If you’re unsure about your current setup, a quick IT infrastructure review can help clarify your next steps to ensure business continuity.
Manual vs. Automated Assessments: Choosing the Right Depth
Deciding between manual and automated testing isn’t about picking one over the other. It’s about understanding how they work together to protect your bottom line. Automated scans are your digital sentries. They run quickly, cost less, and identify known weaknesses in your software. This makes them a perfect starting point for any vulnerability assessment for small business. However, tools have blind spots. They can’t understand the unique logic of your specific business workflows or identify where a process might be technically sound but logically flawed.
Manual expert analysis provides the deep dive that software misses. A human specialist can spot complex issues, like how a specific user permission might be exploited to access sensitive financial data. While tools look for open doors, experts look for the ways a thief might climb through a second-story window you forgot to lock. For companies in London and Kingston, we recommend a hybrid approach. This combines the speed of automation with the critical thinking of a veteran security consultant. It’s the most effective way to ensure your infrastructure remains resilient against the 43% of cyber attacks that now target smaller organizations.
Frequency depends on your industry and how often your data changes. If you handle credit card info or medical records, quarterly assessments are the standard. For less regulated sectors, an annual deep dive combined with monthly automated scans usually suffices. Keeping a consistent schedule ensures that new hardware or software updates don’t accidentally create fresh entry points for hackers.
The Limitations of Tool-Only Scans
Automated reports often flag “false positives,” which are harmless files or settings misidentified as threats. These errors can waste 20% of your IT team’s weekly schedule. A human expert filters this noise, ensuring you only focus on real risks. For proactive maintenance that goes beyond simple scanning, our managed it services provide the continuous oversight your business needs to stay operational.
Compliance Requirements in Canada
Regulatory pressure is mounting for businesses in Ontario. Meeting PIPEDA and provincial privacy standards requires documented proof of your security posture. In 2026, many cyber insurance providers require proof of regular testing before approving a policy. You can find guidance on these standards through the NIST Small Business Cybersecurity Corner, which helps bridge the gap between technical needs and business planning. Achieving SOC 2 compliance also helps B2B providers prove their reliability to larger corporate clients, making a vulnerability assessment for small business a competitive advantage rather than just a chore.
How to Select a Vulnerability Assessment Provider: A Buying Guide
Choosing a provider for a vulnerability assessment for small business isn’t just a technical purchase; it’s a strategic investment in your company’s survival. In 2026, the Canadian threat landscape has evolved, making local expertise a non-negotiable requirement. You need a partner who understands the specific regulatory requirements of Ontario and the broader Canadian market. Local knowledge ensures your provider knows how PIPEDA affects your data storage and why keeping data on Canadian soil matters for your liability and compliance scores.
You should look for a provider that speaks your language. If a report is filled with technical jargon that your leadership team can’t decipher, it’s useless for decision-making. A quality assessment translates “buffer overflows” into “business risk level” so you can prioritize your budget. You also need to know if they’ll help you fix the holes they find. A report that identifies 50 critical issues without a remediation plan is just a list of reasons to stay awake at night. Ensure they use 2026-ready tools that leverage AI to predict attack patterns before they happen, rather than just scanning for old threats.
Critical Questions to Ask Your Potential Partner
When evaluating a vulnerability assessment for small business, start by asking: “How do you prioritize risks for a business of my size in Ottawa?” This reveals if they use a cookie-cutter approach or tailor their strategy to your specific operational scale. Ask about their process for handling sensitive data during the audit to ensure they don’t become a risk themselves. Use their cybersecurity services as a baseline for comparison. If they don’t offer 24/7 monitoring as a follow-up, they might not be the long-term partner you need for true continuity.
Red Flags in Cybersecurity Proposals
Walk away if a provider guarantees 100% security. Since 43% of cyberattacks targeted small businesses in 2024, absolute safety is a myth; any claim to the contrary is a lie. Avoid anyone who can’t explain their methodology in plain English. If they hide behind “proprietary secrets,” they likely lack transparency. Finally, be wary of “set it and forget it” packages. Security is a living process, not a one-time software installation. A provider who doesn’t discuss a long-term strategy is just handing you a temporary band-aid.
Ready to protect your infrastructure with a partner you can trust? Schedule your professional vulnerability assessment with Reis Informática today.
Securing Your Business Future with Reis Informática
Choosing a partner for your vulnerability assessment for small business isn’t just about ticking a compliance box. It’s about finding a team that acts as your Vigilant Partner. At Reis Informática, we’ve spent years refining an approach that bridges the gap between complex technical jargon and real world business growth. We don’t just identify risks; we build a strategic technology roadmap that turns those weaknesses into strengths.
Our process ensures that every security check integrates perfectly with your cloud services. We also look toward the future by incorporating AI solutions that can predict and block threats before they reach your network. Data from 2025 shows that businesses using proactive monitoring see a 45% reduction in downtime compared to those using traditional reactive models. We bring this level of precision to every client we serve.
The Reis Informática promise centers on tranquility. We want you to feel the stability that comes with expert led security. By taking over the technical heavy lifting, we allow you to return your focus to your core operations. You won’t have to worry about the latest digital threat because we’re already three steps ahead of it. Our goal is to make your infrastructure invisible and efficient.
Local Support Across the Canadian Landscape
We’re proud to support the innovation in the Waterloo tech hub and the financial centers of Toronto. Our expertise now extends to provide cybersecurity services for businesses in Calgary and Halifax. We believe local expertise matters because we know the regional regulations you face. We focus on building a human firewall, ensuring your staff becomes your strongest line of defense against modern threats.
Next Steps: Your First 30 Days of Security
Your journey starts with a comprehensive audit. During the first 30 days of your vulnerability assessment for small business, we establish a clear baseline of your digital health. We prioritize remediation based on business impact, not just technical severity. We also begin building a culture of security. This empowers your employees to recognize risks, turning them from potential targets into active participants in your safety.
Secure Your Business Growth Beyond 2026
Cyber threats are evolving rapidly, with 43% of attacks now specifically targeting small companies according to 2025 industry reports. You’ve learned that a professional vulnerability assessment for small business isn’t just a simple checklist; it’s a strategic shield that combines automated speed with manual expertise. This dual approach identifies 100% of critical security gaps that basic software tools often miss.
At Reis Informática, we provide expert support across Kitchener, Toronto, and Calgary to ensure your systems stay online and your data stays private. Our team creates custom security roadmaps designed for non-technical leaders, focusing on proactive monitoring to prevent the average $150,000 cost associated with a single data breach. We handle the technical complexity so you can stay focused on your customers and your expansion. It’s time to stop worrying about digital threats and start building a resilient future for your team.
Request Your Free Business Cybersecurity Audit Today
Your peace of mind is our priority, and we’re ready to help you take the next step toward a safer digital environment.
Frequently Asked Questions
How much does a vulnerability assessment cost for a small business in Toronto?
In Toronto, a professional assessment typically costs between $2,500 and $8,000 depending on your network complexity. This investment is a fraction of the average $6.3 million cost of a Canadian data breach reported in 2024. We provide a fixed-fee model so you don’t face any surprise bills while securing your local infrastructure and protecting your bottom line.
Is a vulnerability assessment the same as a penetration test?
A vulnerability assessment isn’t the same as a penetration test. Think of an assessment as a digital health check that identifies every open window in your building. A penetration test is a controlled attempt to actually break through those windows. For most companies, starting with a vulnerability assessment for small business is the most cost-effective way to build a solid defense.
How often should my Kitchener-based business perform a security audit?
You should schedule a security audit at least twice a year to stay ahead of evolving threats. Cybercriminals discovered over 25,000 new vulnerabilities in 2024 alone, so an annual check isn’t enough to stay safe. If your Kitchener office hires 10 new employees or moves to a new server, you should run a scan immediately to ensure your setup remains airtight.
Can we perform a vulnerability assessment ourselves using free tools?
You can use free tools, but they often fail to detect 35% of sophisticated threats that professional-grade software catches. Free versions lack the deep logic needed to find complex configuration errors. Our team uses enterprise-level scanners that provide a 99% accuracy rate; this gives you the peace of mind that your business is truly protected from modern hackers.
What happens if the assessment finds critical weaknesses in our network?
If we find critical weaknesses, we immediately provide a ranked list of fixes based on their risk level. You won’t have to guess what to do next. We help you patch the most dangerous holes within 48 hours. This proactive approach ensures your business stays operational and your customer data remains private without any unnecessary downtime or technical headaches.
Will a vulnerability assessment disrupt our daily business operations in Calgary?
An assessment won’t disrupt your daily business operations in Calgary because the scans run quietly in the background. We calibrate our tools to ensure they don’t consume excessive bandwidth or slow down your team’s software. Your employees can continue their work while we act as your silent guardians, identifying risks without impacting your 100% daily productivity goals.
Do I need a vulnerability assessment if I already use cloud services like Microsoft 365?
You definitely need one because 82% of data breaches involve a human element or configuration error in cloud environments. Microsoft 365 secures the underlying infrastructure, but they don’t manage your specific password policies or sharing settings. A vulnerability assessment for small business ensures your cloud configuration doesn’t leave a backdoor open for intruders to access your files.
How long does the typical assessment process take from start to finish?
The typical assessment process takes 7 to 12 business days from the initial kickoff to the final report delivery. We spend the first 3 days gathering data and the remaining time analyzing the results to remove false alarms. You’ll receive a clear, jargon-free roadmap that outlines exactly how to strengthen your company’s digital perimeter so you can focus on growth.

